
Five of them allow remote compromise of the IoT gadgets, so attackers can intercept video feeds and more.

ThreatList: Fewer Big DDoS Attacks in Q3, Overall Rate Holds Steady

5G Security System Design for All Ages
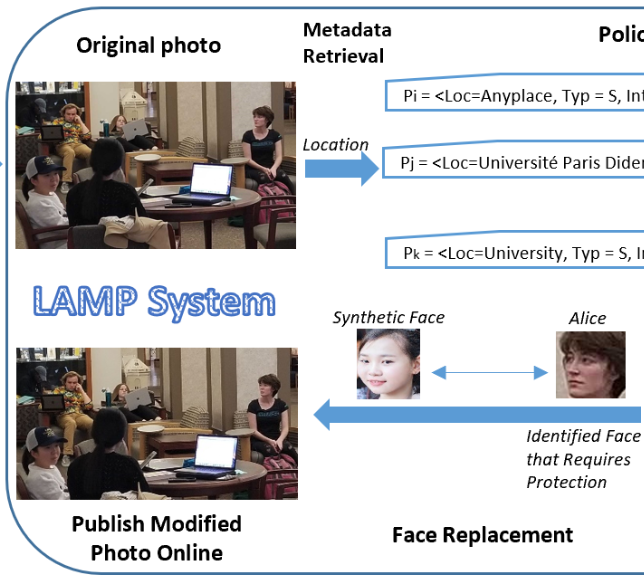
CIVA Lab Publications
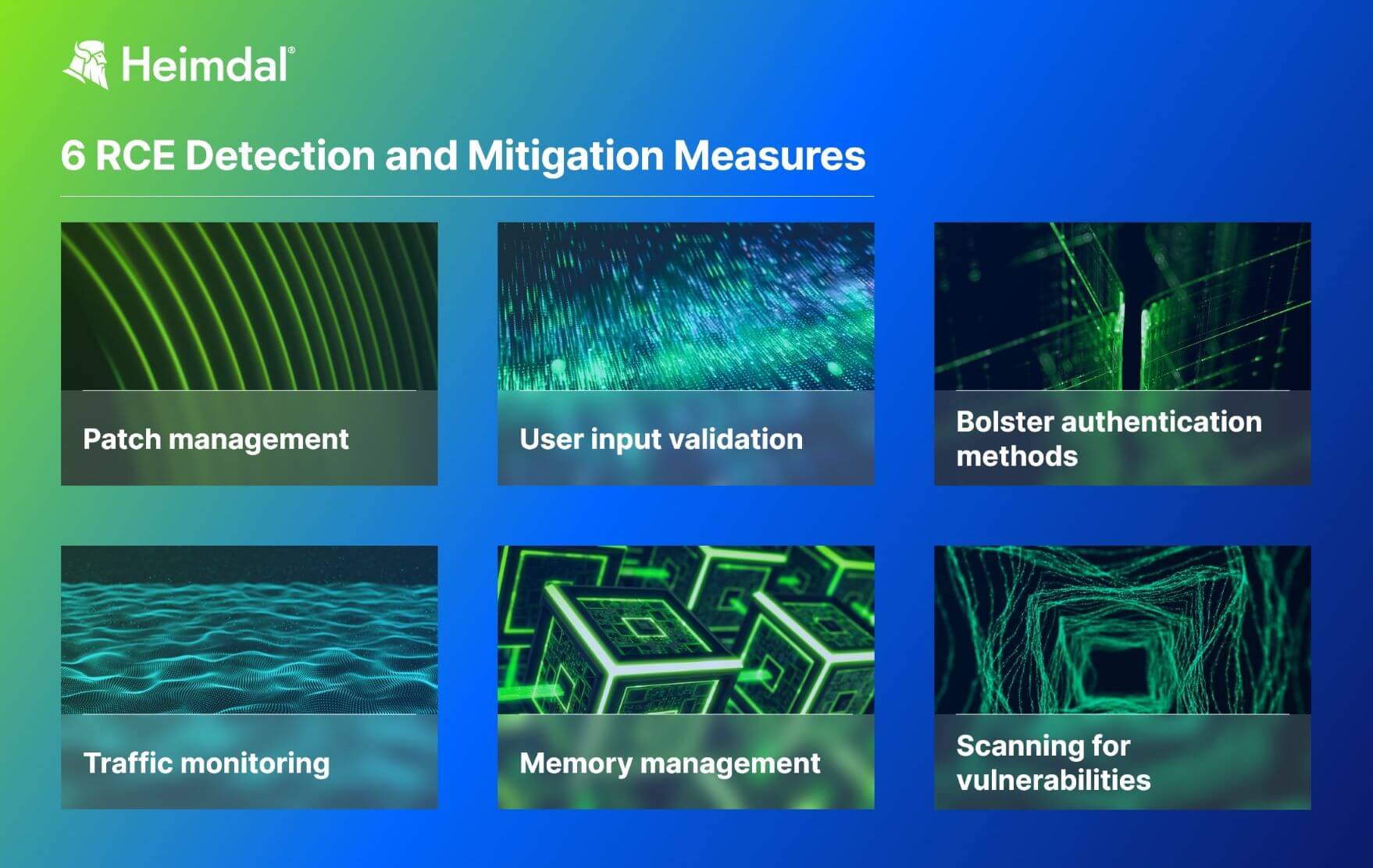
What Is a Remote Code Execution Attack? Definition, Risks, and Mitigation Measures
GitHub - alienatedsec/yi-hack-v5: Even newer Custom Firmware for Xiaomi Cameras based on Hi3518ev200 Chipset. It includes free RTSP, ONVIF and other improvements based on the work by roleoroleo
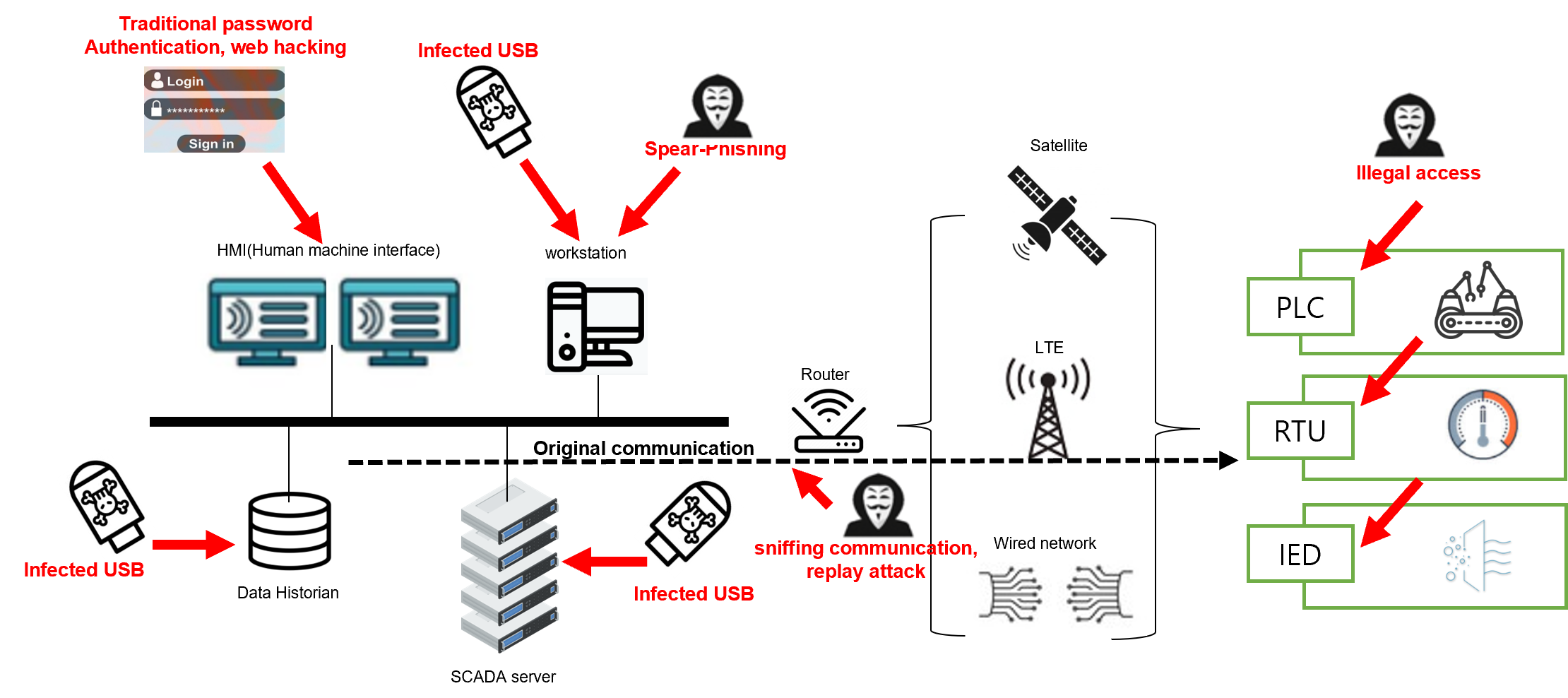
Part 1) Key security vulnerabilities in IoT environment and how to effectively counteract them

Yi IoT Home Camera Riddled with Code-Execution Vulnerabilities

A systematic review of the purposes of Blockchain and fog computing integration: classification and open issues, Journal of Cloud Computing
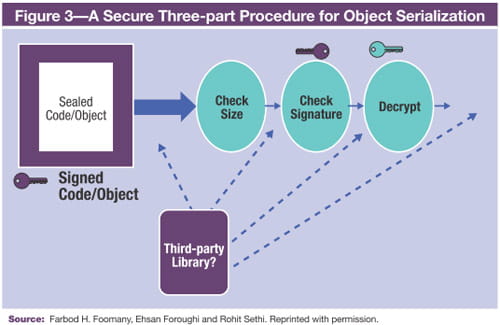
Inquiring Into Security Requirements of Remote Code Execution for IoT Devices

Human Digital Twin in the context of Industry 5.0 - ScienceDirect






